Hybrid Cloud Security: Balancing Business Agility and Protection
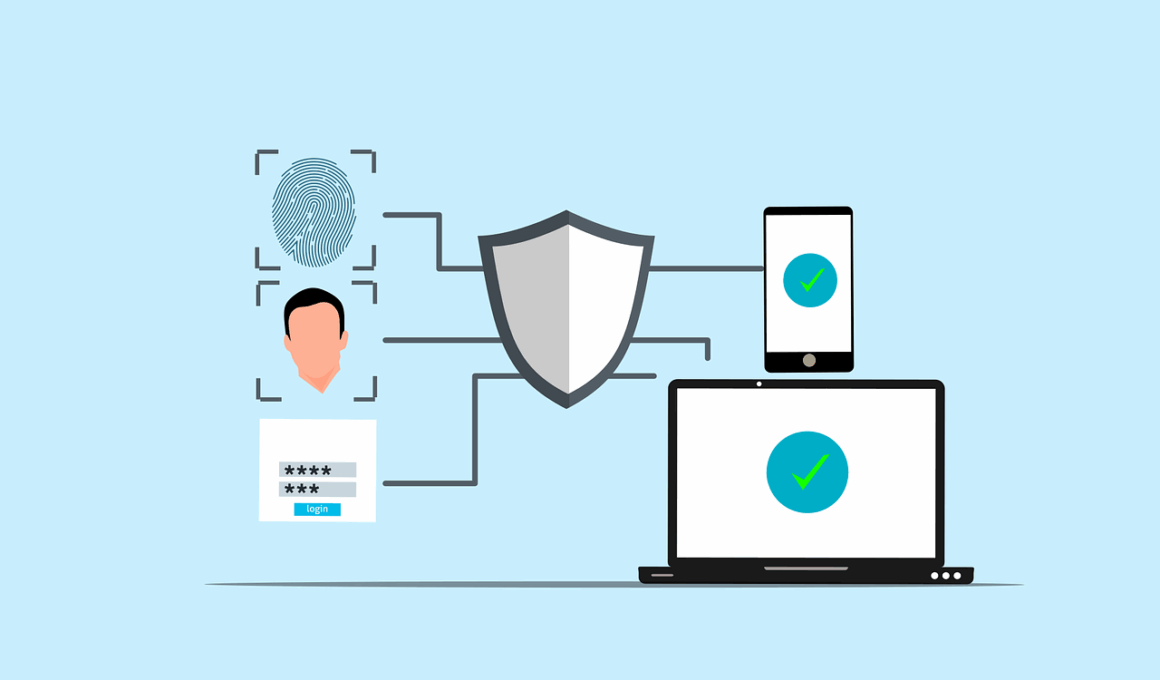
As businesses increasingly adopt hybrid cloud environments, security becomes a primary concern. These environments combine private and public cloud components, offering flexibility and scalability while also introducing unique security challenges. Organizations must implement a robust security framework that addresses data privacy, compliance, and available resources. This framework should encompass strong encryption protocols for data at rest and in transit to prevent unauthorized access. Regular security audits must identify vulnerabilities and misconfigurations. Security measures also need to accommodate dynamic workloads which change frequently. Additionally, businesses must train their staff on emerging threats such as phishing attacks that can target cloud applications. By implementing multi-factor authentication, organizations can enhance their account security significantly. Lastly, aligning on service level agreements (SLAs) with cloud providers can further mitigate risks. As cyber threats evolve, a multi-faceted approach combining technology, employee training, and best practices becomes paramount. In this rapidly changing landscape, having a dedicated team focused on cloud security can make a substantial difference in minimizing risks, preserving customer trust, and maintaining competitive advantages.
One of the pivotal aspects of hybrid cloud security is the integration of traditional security practices with cloud-native tools. Businesses often struggle to understand the distinctions between the security requirements of public and private clouds. Employing a unified security management approach eliminates silos and provides visibility across the entire architecture. This can be achieved by utilizing security information and event management (SIEM) systems which aggregate data from multiple sources. Moreover, companies must consider the implications of shared responsibility in a hybrid cloud. Cloud service providers secure the infrastructure, but businesses are responsible for securing their data and applications. Therefore, organizations need to define their security policies carefully and ensure compliance with industry regulations. Implementing least privilege access protocols ensures that users have just the right amount of access needed to perform their tasks. Additionally, automating security updates and configurations is essential in reducing human error. This approach allows security teams to focus on more strategic tasks, such as threat modeling and incident response. Effectively navigating the complexities of hybrid cloud security sends a strong message to stakeholders about the commitment to protect data and maintain operational integrity.
Challenges in Hybrid Cloud Security
With benefits come numerous challenges, especially concerning compliance and data governance across mixed environments. As businesses utilize multiple cloud services, navigating different regulations can create confusion and uncertainty. Compliance with standards like GDPR, HIPAA, or PCI DSS becomes challenging since different jurisdictions impose unique requirements. Businesses must catalog their data to ensure proper handling per regulatory expectations. Data governance policies must also address how data is transferred between clouds, particularly if sensitive information is involved. It’s vital to understand how data loss prevention (DLP) technologies work across cloud boundaries. Effective monitoring systems should detect any anomalies in data traffic, potentially signaling a breach. Regular risk assessments are crucial to identify which assets are most vulnerable in a hybrid setup. Third-party integrations present another layer of risk, necessitating thorough vetting of those partners. Organizations must ensure that all third-party vendors adhere to similar security measures as they do. In contrast to legacy systems that might offer uniformity, hybrid environments often require tailor-made solutions to adequately address distinct security challenges that arise.
Another critical concern for hybrid cloud security is ensuring the continuity of access and operations amidst potential disruptions. Many businesses have realized the importance of disaster recovery plans that complement their hybrid strategies. These plans must detail specific incident response protocols for various types of threats, including cyber-attacks and natural disasters. Organizations should consider geolocation for their data recovery strategies, ensuring redundancy across multiple regions. Testing these recovery processes periodically is essential to guarantee operational readiness. Furthermore, cloud errors and outages can happen; thus, businesses must have solutions that can automatically re-route traffic and workloads during disruptions. Resilience in the face of these challenges is vital for maintaining customer trust. Additionally, stakeholders should understand the risks involved in deviating from established procedures during crises. Documentation, training, and regular reviews of incident response plans contribute to a culture of preparedness within the organization. In the evolving landscape of cloud computing, maintaining operational continuity while protecting assets becomes one of the key focus areas for business leaders. When each layer of security is accounted for, organizations stand a better chance against delays and financial losses.
Technologies Supporting Hybrid Cloud Security
Technological advancements play a significant role in enhancing the security of hybrid cloud infrastructures. Firewalls, intrusion detection systems (IDS), and behavioral analytics tools are essential in identifying and mitigating threats. Next-generation firewalls (NGFW) that integrate application awareness greatly improve network security, facilitating control over traffic patterns based on applications rather than ports. Artificial intelligence (AI) and machine learning (ML) technologies are also making strides in the cybersecurity realm. By using these tools, organizations can analyze vast amounts of data to recognize threat patterns and proactively address potential vulnerabilities. Furthermore, implementing a zero-trust architecture ensures that verification is required from everyone attempting to access resources, regardless of whether they are inside or outside the network perimeter. This model greatly reduces the attack surface and increases overall security. Virtual Private Networks (VPNs) are crucial for encrypting data transmissions, particularly for remote workforces. It’s also essential to implement secure application programming interfaces (APIs) since they often serve as gateways to sensitive resources. As businesses invest in these technologies, aligning them with updated policies ensures a holistic approach to hybrid cloud security that is proactive in nature.
Building a culture of security within an organization is foundational to successful hybrid cloud security. Employees must understand the significance of cybersecurity and actively participate in security initiatives. Regular training sessions that cover topics like recognizing phishing attempts, using secure passwords, and reporting incidents equip staff with necessary skills. Promoting open lines of communication between the security team and other departments reinforces accountability. Security awareness campaigns should include information on the latest threats and secure behaviors. Also, organizations should encourage employees to share their experiences or concerns about security matters, promoting a collective responsibility. Utilizing gamification techniques for training can increase engagement and knowledge retention. Essential tools that help manage and monitor user behaviors, such as privileged access management (PAM), can mitigate risks posed by insider threats. Moreover, periodic evaluations of staff knowledge and skills showcase the effectiveness of training programs. By fostering a security-focused culture, businesses become more resilient against potential breaches. Stakeholder confidence grows when companies demonstrate their commitment to protecting sensitive information and ensuring business continuity within hybrid cloud environments.
The Future of Hybrid Cloud Security
As the digital landscape continues to evolve, the future of hybrid cloud security will undoubtedly bring new challenges and innovations. Cloud technology adoption will accelerate, compounding the need for robust security measures. Advances in quantum encryption and blockchain technologies promise to enhance security protocols in ways previously thought unrealizable. Quantum encryption exploits the principles of quantum mechanics to create unbreakable security for transmitted data, while blockchain can provide decentralized validation pathways. Businesses that are early adopters of these technologies may lead in competitive advantage. However, as systems grow more complex, the potential for new vulnerabilities increases, necessitating continuous investment and adaptation in security strategies. Compliance regulations will also likely evolve in conjunction with technological advancements, introducing new challenges to maintain adherence. Collaborative partnerships between businesses and cybersecurity firms will become commonplace to bolster defense mechanisms against cyber threats. By leveraging shared intelligence and resources effectively, organizations can address vulnerabilities dynamically. Ultimately, the notion of securing hybrid cloud environments will shift from reactive to proactive, illustrating how essential adaptive strategies are in an ever-changing technological world.
Looking ahead, businesses using hybrid cloud services must prioritize proactive security measures and holistic strategies. Cybersecurity policies should be revisited frequently to ensure they remain relevant and effective. Embracing emerging technologies like AI, machine learning, and automation can address high volumes of cyber threats efficiently. Organizations should integrate security tools that will enable streamlined workflows and enhance visibility across their cloud environments. Additionally, maintaining relationships with trusted security partners can lead to valuable insights and up-to-date threat intelligence. Following best practices for incident response, organizations should prepare for rapid identification and containment of security breaches. Continuous improvement of hybrid cloud security mandates a responsive approach as threats evolve. As organizations invest in security talent, developing in-house expertise will also be crucial in this dynamic environment. Cybersecurity training should not be a one-time initiative but rather an ongoing commitment, instilling a culture of vigilance. Stakeholders need reassurance that their data remains protected as businesses continue to navigate toward increased reliance on hybrid cloud infrastructures. This proactive stance allows for sustainable growth while mitigating risks associated with the ever-changing cybersecurity landscape.