Managing Insider Threats in BYOD Workplaces
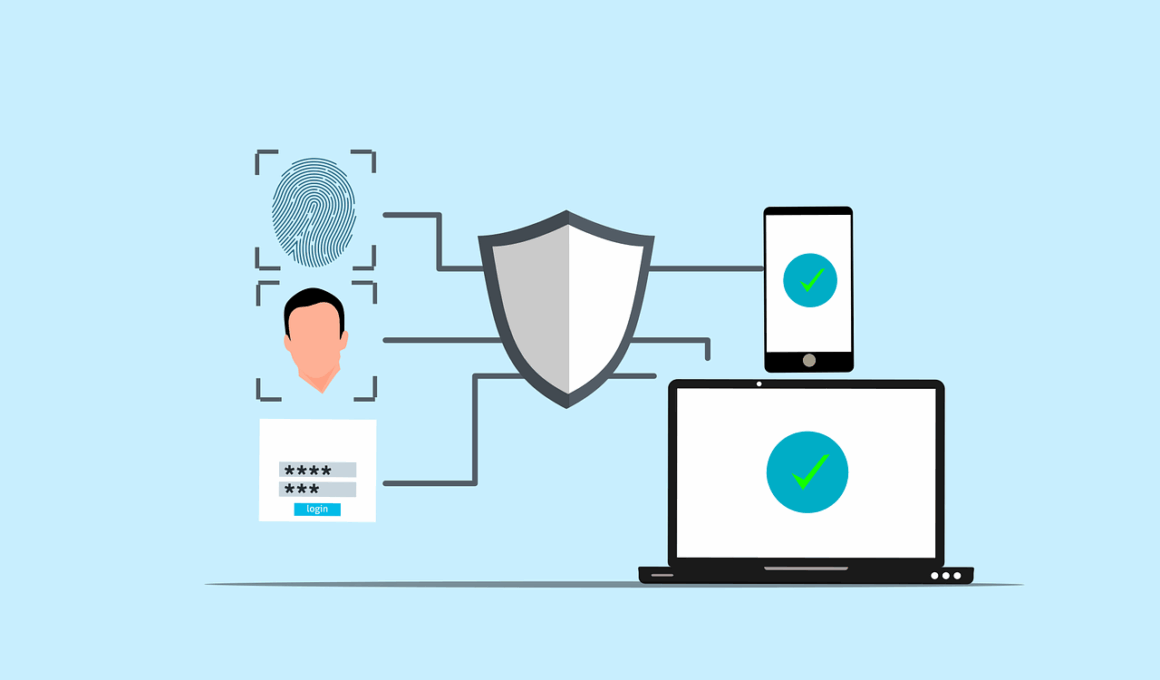
In today’s digital landscape, businesses often adopt Bring Your Own Device (BYOD) policies to enhance productivity and employee satisfaction. BYOD allows employees to utilize personal devices for work tasks, which can offer significant benefits but also presents considerable cybersecurity risks. Insider threats—involving employees misusing their device access to company data—are particularly hard to manage. Organizations must ensure that appropriate security measures are in place, including robust data security protocols and device management practices. A comprehensive strategy should also address employee education, advocating for awareness about the potential security risks involved with personal devices. Establishing clear guidelines can help mitigate risks associated with unauthorized access and potential data breaches. Further, using mobile device management (MDM) solutions enables businesses to enforce security policies effectively. Integrating endpoint security solutions adds additional layers of protection. The balance between access and security is crucial to helping safeguard sensitive company information while still allowing employees the flexibility they desire. Overall, addressing insider threats within BYOD environments necessitates a structured approach that combines technology, policies, and education to ensure an optimal security posture while promoting user comfort.
One of the core concerns when managing insider threats in BYOD workplaces is the nature of device usage. Employees may unintentionally or intentionally misuse their devices to access sensitive data. Implementing access controls is vital to safeguard against such threats. For instance, employing role-based access control (RBAC) can provide employees with restricted access to confidential information based on their job roles. This limits the exposure of vital information only to authorized personnel reducing potential misuse. Moreover, organizations should consider conducting regular audits and network monitoring to identify unusual activity patterns that may indicate insider threats. Instituting a zero-trust model aligns well with these controls, where verification of user identity is essential regardless of their location. Regular training sessions can foster a culture of security awareness, encouraging employees to recognize potentially harmful behavior and reporting any suspicious activities. Furthermore, maintaining an incident response plan ensures quick actions in case of a security breach. Cultivating an environment where security is a communal responsibility helps unify efforts to combat insider threats effectively, thereby boosting overall workplace security in the BYOD landscape.
Clear communication is necessary to counter insider threats effectively in BYOD environments. It is important for organizations to develop and enforce a comprehensive BYOD policy that details the acceptable use of personal devices within the workplace. This policy should outline the responsibilities of employees regarding data security and the repercussions of policy violations. Informing employees about the importance of securing their devices and safeguarding sensitive information can significantly mitigate risks. Up-to-date information on acceptable software and application usage can also be beneficial. Additionally, implementing encryption for data at rest and in transit ensures that sensitive information remains protected, even if devices are lost or compromised. Employers must also evaluate third-party applications and tools that employees intend to use to ensure they comply with company security standards. Regular reviews and updates of the BYOD policy can strengthen the organization’s security posture. Encouraging open dialogue about security issues creates an atmosphere of trust. Employees need to feel comfortable discussing potential risks without fear of reprimand. A proactive approach towards developing clear communication channels enhances a firm footing against the threats posed by insider malfeasance in the BYOD setup.
Role of Technology in Mitigating Insider Threats
Technological solutions play a pivotal role in combating insider threats within BYOD workplaces. Organizations should leverage various tools to ensure that personal devices comply with established security protocols effectively. Mobile Application Management (MAM) solutions can help manage and secure applications, providing another layer of defense in an employee’s own device. Additionally, the use of Mobile Device Management (MDM) allows IT departments to enforce security policies across all devices. Ensuring that devices meet organizational security standards becomes essential for protecting sensitive information accessed through personal devices. Intrusion detection and prevention systems (IDPS) also contribute significantly to identifying potential security breaches in real time, alerting IT teams to any irregularities. By integrating machine learning and analytics, organizations can anticipate potential insider threats before they escalate. Furthermore, collaborating with cybersecurity professionals to conduct thorough assessments can help identify risks specific to the organization’s environment. A well-established cybersecurity infrastructure allows businesses to stay steps ahead of potential vulnerabilities. Adopting a proactive approach toward technology ensures the integrity and security of organizational data within the BYOD framework.
Another critical aspect of managing insider threats in BYOD workplaces involves fostering a security-focused culture within the organization. Encouraging employees to uphold best practices in cybersecurity can significantly reduce risks associated with personal device usage. Offering regular training sessions on identifying phishing attacks, managing passwords, and securing personal devices empowers employees with the skills they need to act as the first line of defense. Building trust within teams allows employees to feel that they are valued contributors to the organization’s security efforts. Gamifying security education can enhance employee engagement, making learning enjoyable and memorable. Additionally, fostering open discussions about security threats can encourage employees to share their experiences and strategies for minimizing risks. Recognizing those who excel at practicing security measures fosters a culture of accountability and reinforces the importance of safeguarding sensitive information. Organizations should emphasize that security protocols are not merely rules but crucial guidelines designed to protect the company, the employees, and its clients. A continuous learning environment enables businesses to adapt to evolving security challenges. Thus, cultivating a security-conscious culture is integral in addressing insider threats successfully.
Regular assessment and updates are also crucial components of maintaining robust security protocols to combat insider threats within BYOD settings. Organizations should frequently re-evaluate their BYOD policies to ensure they align with the evolving technological landscape and emerging threats. It is essential to involve employees in these assessments, gathering valuable feedback that can help in refining security measures. Moreover, conducting penetration tests can simulate insider threats, providing insights into potential vulnerabilities. Reviewing incident response plans ensures that employees know how to react in case of a data breach and can mitigate damage effectively. Keeping security software updated is just as vital as maintaining the overall IT infrastructure to ensure optimal protection against evolving threats. Changes in compliance regulations should prompt a review of existing policies to ensure they adhere to legal requirements relevant to data protection. Collaborating with industry partners to share threat intelligence can provide organizations with updates on prevalent risks. Thus, fostering a culture of introspection and adaptability while ensuring employees remain at the forefront of security measures can significantly enhance an organization’s security chapter.
Importance of Incident Response Planning
Having a robust incident response plan is essential for addressing insider threats effectively in BYOD workplaces. Such plans are vital to minimize the impact of any security breach that may arise. Organizations should create a clearly defined incident response framework that outlines specific roles and responsibilities. This framework should include established procedures for reporting suspicious activities and managing potential breaches. Quick response times can significantly reduce the potential damages and unforeseen repercussions associated with insider threats. Training employees on their role in the incident response can enhance preparedness significantly. Additionally, conducting regular drills will prepare teams for potential real-world scenarios, ensuring they respond efficiently. Organizations must integrate comprehensive communication protocols within their incident response strategy, ensuring all members are kept informed throughout the process. Post-incident reviews are equally important to analyze the response, identify weaknesses, and apply necessary learnings for future improvements. Engaging external specialists to assess the effectiveness of the incident response continuously allows organizations to adapt their plans as necessary. Therefore, creating a solid incident response plan equips organizations to handle insider threats more proactively, preserving their overall integrity and resilience.
Ultimately, managing insider threats within BYOD workplaces is a multifaceted challenge. It involves addressing technology, policies, culture, training, and incident response planning, all while acknowledging the complexities that come with employees using personal devices for work purposes. A balanced approach that considers both the advantages and risks of BYOD is essential for a secure workplace. Organizations need to recognize that insider threats can stem from various motivations, including negligence, malice, or unawareness. Therefore, fostering trust, communication, and accountability among employees is vital to the overall strategy. Additionally, by remaining vigilant and proactive in implementing security measures, businesses can create a robust security environment surrounding BYOD practices. In this increasingly digital age, organizations cannot afford to overlook the potential dangers posed by insider threats. They must embrace a comprehensive strategy that incorporates technological solutions, employee engagement, and continuous improvements to minimize risks effectively. Failing to do so can result in severe consequences, including data breaches and the loss of customer trust. Thus, the path to managing insider threats requires intentional focus and commitment across all organization levels.