Zero Trust Architecture for Remote Workforces: Securing Distributed Teams
The rise of remote work has changed how businesses approach cybersecurity. Traditional security models, which rely on perimeter defenses, have become inadequate in an environment where employees access resources from various locations. Zero Trust Architecture (ZTA) presents a shift in this paradigm by enforcing strict access controls regardless of the user’s location. This model assumes that threats may exist both inside and outside the network, prompting a reevaluation of security frameworks. Within a Zero Trust model, all requests are treated as if they originate from an open network. By applying the principle of least privilege, organizations can minimize access to only what users need. Additionally, Zero Trust enables continuous monitoring and validation of user identities and devices. Such scrutiny ensures that suspicious activities are detected early, reducing the risk of data breaches. Implementing ZTA is essential for organizations embracing remote work, as it fosters a mindset that prioritizes security while enabling productivity. Ultimately, businesses must understand the importance of adopting ZTA in a distributed workforce to safeguard sensitive information effectively.
The Core Principles of Zero Trust Architecture
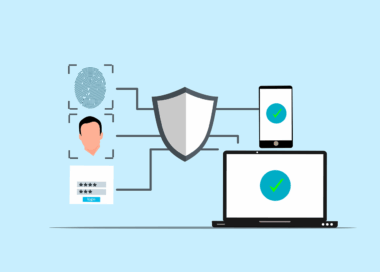
Zero Trust Architecture is founded on several core principles, ensuring that organizations effectively secure their systems. One of the most significant tenets is “never trust, always verify,” which emphasizes continuous authentication and authorization of users and devices. This philosophy mandates that access to resources is granted only after thorough verification. Another crucial principle is segmentation, which involves dividing the network into smaller, manageable units. This limits user access strictly to the resources necessary for their roles, shielding sensitive areas from potential attacks. Furthermore, ZTA employs robust identity management tools to ensure that access rights are closely monitored and adjusted as per dynamic needs. The integration of multi-factor authentication (MFA) adds another layer of security, making it more challenging for unauthorized users to gain access. Consequently, implementing these principles can help organizations anticipate and neutralize potential threats before they escalate. The Zero Trust model aims to create a security environment where every transaction is scrutinized and verified, reducing the attack surface in increasingly complex digital landscapes. Adopting these principles strengthens organizations’ defenses against evolving cybersecurity threats.
The importance of implementing a Zero Trust Architecture can be highlighted through its capabilities in continuously monitoring network traffic. Traditional security measures often fail to scrutinize behaviors within the network, allowing security breaches to go unnoticed. With ZTA, organizations leverage advanced analytics and artificial intelligence to identify anomalies. By constructing baselines of regular user and device behavior, ZTA systems can flag unusual activities swiftly. Anomalies may signal potential threats, enabling security teams to respond proactively. This capability is crucial as cybercriminals increasingly exploit human vulnerabilities and poorly secured devices. Moreover, the prevalence of advanced persistent threats necessitates a robust response strategy. By analyzing traffic patterns, organizations can optimize their security posture against such threats. Furthermore, incident response plans within a Zero Trust framework are designed to be agile and efficient, emphasizing rapid containment of breaches. The approach minimizes damage and ensures quick recovery, sustaining business continuity. Continuous adaptation to emerging threats is also a cornerstone of ZTA. Thus, organizations utilizing ZTA can remain resilient in the face of challenges posed by a rapidly evolving cybersecurity landscape.
Challenges in Implementing Zero Trust Architecture
Despite its advantages, transitioning to Zero Trust Architecture is not without challenges. Organizations face resistance from employees accustomed to traditional network security practices. Changing user behavior and instilling a security-first mindset requires continuous training and engagement. Furthermore, implementing Zero Trust often necessitates significant investment in innovative technologies, which can strain budgets, especially for small to medium enterprises. Integrating existing systems with ZTA can also prove complicated, as legacy applications may not align with Zero Trust principles. This integration requires a thorough analysis of the organization’s current infrastructure and security tools, potentially leading to unforeseen complications. Additionally, establishing efficient access controls demands collaboration across departments, which can complicate decision-making processes. Nonetheless, the long-term benefits of ZTA can outweigh these hurdles, particularly regarding risk mitigation and data protection. To alleviate implementation challenges, organizations must develop clear strategies that address potential resistance while emphasizing training and awareness. Effective collaboration across teams ensures that the transition to Zero Trust becomes a comprehensive and inclusive effort. This integrated approach lays the groundwork for successfully adopting ZTA in organizations, thereby enhancing overall cybersecurity resilience.
Furthermore, evaluating and measuring the success of a Zero Trust Architecture implementation is crucial for organizations. Establishing clear performance metrics allows businesses to assess the effectiveness of their security posture. Key indicators include incident response time, the number of detected breaches, and the overall reduction of unauthorized access attempts. Regular audits of access controls and user behavior analytics contribute valuable insights into potential vulnerabilities. Continuous feedback loops also help refine ZTA measures, ensuring they evolve alongside emerging threats. Additionally, organizations must consistently review and update their policies to match the changing dynamics of technology and workforce patterns. Keeping abreast of industry best practices and regulatory requirements further strengthens the ZTA framework. Engaging with cybersecurity professionals and consulting firms can provide organizations with expert guidance for optimizing their security strategies. As remote work continues to dominate the business landscape, organizations that prioritize monitoring and refining their Zero Trust measures position themselves for long-term success. Ultimately, the commitment to a proactive security strategy encapsulated by ZTA fosters a robust defense against the complexities of contemporary cybersecurity threats.
Conclusion: Embracing Zero Trust for Future Safeguarding
In conclusion, embracing Zero Trust Architecture is essential for businesses aiming to secure distributed teams in a remote work environment. With the traditional perimeter-based defense becoming obsolete, ZTA introduces a comprehensive methodology that significantly mitigates cybersecurity risks. Its focus on user verification, continuous monitoring, and resource segmentation offers a proactive approach to cybersecurity challenges. However, businesses must recognize the potential challenges in implementing such a model. By addressing employee resistance, investing in training, and leveraging the right technologies, organizations can facilitate a successful transition to Zero Trust. The adaptability and resilience inherent in ZTA are crucial in today’s fluid work arrangements, ensuring that organizations remain vigilant against evolving threats. As cybercriminals continue to innovate, organizations must be proactive in their security measures. This commitment not only safeguards sensitive information but also fosters a culture of security awareness across the workforce. Ultimately, implementing ZTA is not just an IT responsibility but a collective business imperative. The era of remote work demands heightened security frameworks, and Zero Trust Architecture stands out as an integral component of robust cybersecurity strategies.
In summary, organizations that successfully adopt and integrate Zero Trust principles position themselves favorably in the digital landscape filled with risks. The evolution towards flexible work arrangements amplifies the need for stringent security frameworks that can withstand attacks from sophisticated cyber adversaries. Leveraging tools that support Zero Trust allows organizations to gain visibility into their networks while ensuring that data remains protected regardless of its location. Additionally, this approach fosters a strong identity and access management posture, vital for mitigating risks associated with remote work’s inherent vulnerabilities. By maintaining a commitment to ZTA, organizations can fortify their defenses, ensuring they remain secure in an ever-changing environment. The landscape of cybersecurity will continue to evolve, and businesses must stay ahead of the curve. Continuous improvement in security measures, centered around Zero Trust, ensures that organizations can navigate the complexities of modern threats. As they enhance their security strategies, businesses will see greater resilience against attacks and improved operational continuity, enabling them to thrive in a digitally-driven world. A robust Zero Trust framework becomes not only a competitive advantage but a necessity in protecting organizational assets.