Security Challenges and Solutions in Mobile Commerce
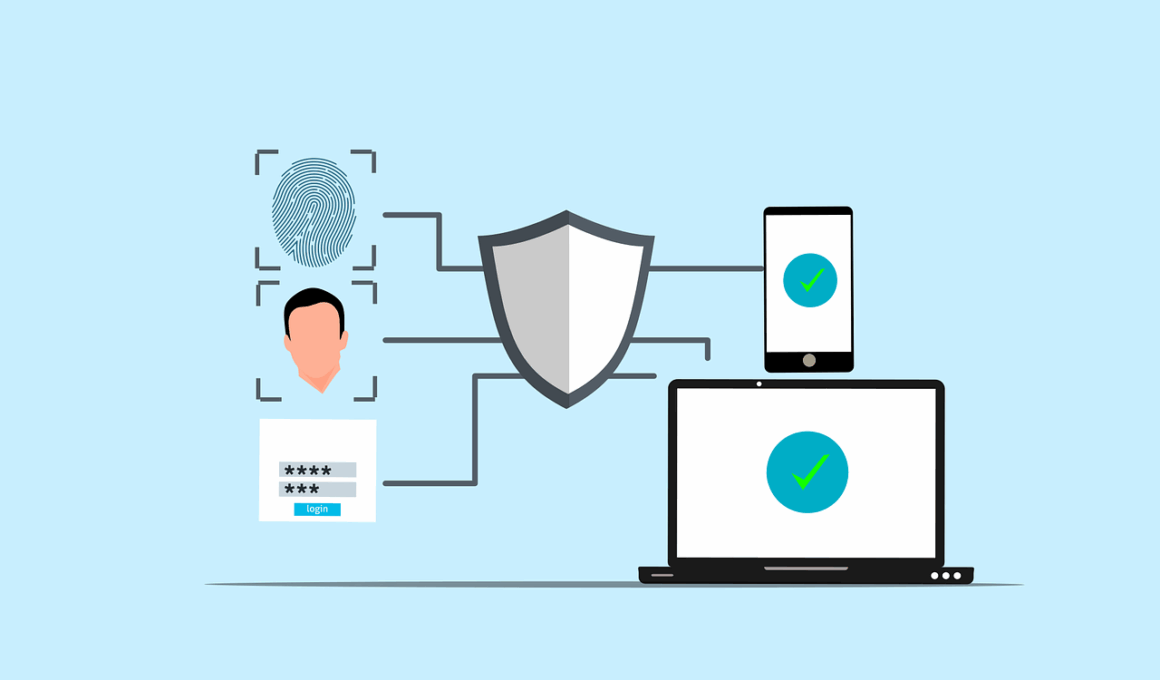
Mobile commerce, commonly known as m-commerce, has revolutionized the way consumers shop online. However, it presents several security challenges that need addressing to ensure consumer trust and safety. With rapid advancements in technology, m-commerce transactions are evolving, leading to increased incidences of fraud, identity theft, and data breaches. One significant challenge is the use of unsecure public Wi-Fi networks, which allow malicious actors to intercept sensitive information such as credit card details. Furthermore, the proliferation of mobile applications has led to a lack of uniform security protocols, making them susceptible to hacking and other cyber threats. Ensuring that mobile devices are protected against malware and viruses is also crucial. Businesses must invest in robust security infrastructure to counteract these threats, instilling confidence in consumers. This includes employing encryption technologies, multi-factor authentication, and regular security audits. Additionally, educating consumers on best practices for secure shopping can significantly minimize risks. By addressing these challenges proactively, businesses can not only safeguard their operations but also enhance user experience, resulting in increased sales and customer loyalty.
Understanding the Threat Landscape
The threat landscape for m-commerce is wide and varied, encompassing issues like phishing attacks, man-in-the-middle attacks, and rogue applications designed to exploit vulnerable users. Phishing, particularly through SMS or email, lures consumers into providing personal and financial information unwittingly. As mobile devices become more integral to daily life, such threats are becoming increasingly sophisticated. Additionally, social engineering tactics are frequently employed by cybercriminals to manipulate consumers into revealing sensitive information. These threats highlight the need for businesses to be vigilant in implementing multi-layered security strategies. Another major concern arises from unclaimed mobile devices and their data storage capacity. If a device is lost or stolen, all sensitive information saved on it could potentially be accessed. Organizations must enforce stringent policies regarding device management, such as remote wipe capabilities and tracking systems. Educating employees about potential threats is critical in mitigating risks as well. By developing an awareness culture regarding mobile security threats, businesses can help protect both their assets and their customers, effectively reducing vulnerabilities in their m-commerce operations.
Another security challenge stems from the use of mobile payment systems, which can vary greatly in security levels between providers. While established payment systems typically offer secure transaction methods, newer or less recognized platforms may not have stringent security measures in place. Users utilizing these options may be putting their personal information at risk without realizing it. Businesses embracing mobile commerce must be discerning when adopting payment systems, opting for those known for robust security protocols. In addition, keeping software up-to-date is vital as security patches and updates help close vulnerabilities. End-users should also be informed on how to check for secure payments, looking for indicators such as HTTPS in URLs or recognizable security badges. Furthermore, properly training staff on how to handle transactions and manage customer data through mobile systems is essential. Establishing a culture of security responsiveness can ensure that employees understand the critical importance of data protection. Regularly reviewing payment system performance and security measures will allow companies to remain one step ahead of potential threats, fostering a safer environment for m-commerce.
Data privacy is another significant issue in the realm of m-commerce. Customers often share a wealth of personal information, from address details to financial data, making it crucial for companies to prioritize the protection of this sensitive information. Compliance with data protection regulations becomes imperative as businesses operate in increasingly stringent legal environments. Regulations such as the General Data Protection Regulation (GDPR) mandate that firms take proactive measures to safeguard consumer data and transparently communicate privacy policies. Inadequate compliance can lead to hefty fines and loss of customer trust. To address these challenges, m-commerce businesses need to employ privacy by design methods, ensuring that new applications are built with robust security measures. It is vital to regularly conduct privacy impact assessments to identify and mitigate any potential risks. Furthermore, businesses should ensure that customer data is only retained for necessary durations, while also offering consumers the ability to opt out of data collection if desired. By emphasizing data privacy and transparent practices, firms can create a more trustworthy and appealing mobile commerce experience for consumers.
In addition to compliance and privacy concerns, educating consumers about the security features of mobile commerce is essential for building trust. Users are often unaware of how to protect their personal information effectively while shopping online. Therefore, businesses should conduct promotional campaigns to raise awareness about safe shopping practices. They can leverage blog articles, social media content, and in-app notifications highlighting tips for secure transactions. Offering detailed explanations about how m-commerce platforms use advanced technologies to protect users can also foster customer confidence. Moreover, companies could provide regular updates about any changes in security protocols or potential threats within their services. By encouraging consumers to adopt behaviors like regularly updating their passwords and using strong, unique passwords, businesses can play a vital role in enhancing overall security. Additionally, customer support should be easily accessible to address security inquiries. Clear communication channels can facilitate an environment where users feel informed and supported. Implementing a robust consumer education strategy helps in fostering a security-centric mindset that resonates with m-commerce users, encouraging safer transaction practices.
Another critical factor to consider for m-commerce success is the importance of end-to-end encryption. This technology ensures that data exchanged between the user’s device and the server remains confidential and protected from potential breaches or leaks. By using encryption, businesses can ensure that sensitive customer information, such as payment details, is not intercepted during transmission. It is vital for any mobile commerce platform to implement secure SSL/TLS protocols to achieve this level of security, as they encrypt data and create secure connections. Moreover, m-commerce providers must continuously monitor and test their systems for vulnerabilities that could be exploited. Regular penetration tests can reveal potential security flaws that need addressing to maintain a secure environment. Companies should also consider employing third-party security services that specialize in mobile commerce security to gain better insights and recommendations for improvement. Implementing a proactive security approach and embracing encryption will safeguard customer data, creating a reliable shopping environment. This commitment to security can not only lead to higher customer satisfaction but also enhance overall business reputation within the competitive m-commerce landscape.
Finally, it is essential that m-commerce platforms focus on continuous improvement and innovation in their security strategies. As technology evolves, so do the tactics used by cybercriminals, necessitating businesses to stay ahead of the curve. A one-time security solution may not suffice, as emerging threats will require dynamic and adaptive approaches. Organizations should allocate resources towards research and development for security technologies that can enhance existing frameworks. Partnering with security experts can provide valuable insights into effective practices and tools to safeguard consumer data. Additionally, providing employees with ongoing training in the latest security measures and incident response tactics creates a more resilient workforce. Implementing incident response plans ensures that businesses can quickly address security breaches should they occur, reducing damage to the organization and their customers. By fostering a culture of continuous learning, companies can better prepare for new challenges and protect their consumers. Committing to security as an integral aspect of business strategy ultimately strengthens consumer trust while driving loyalty in the competitive world of mobile commerce.
This is an additional paragraph with exactly 190 words that doesn’t follow the previous paragraph style.